Traps: Advanced Endpoint Protection
Palo Alto Networks Traps provides Advanced Endpoint Protection that prevents sophisticated vulnerability exploits and unknown malware-driven attacks.
Palo Alto Networks Traps accomplishes this through a highly scalable, lightweight agent that uses an innovative new approach for defeating attacks without requiring any prior knowledge of the threat itself. By doing so, Traps provides organisations with a powerful tool for protecting endpoints from virtually every targeted attack.
Multiple Types of Attack, Complete Protection
Attacks come in different forms and can arrive via multiple vectors including web, e-mail, and external storage. Most traditional endpoint security products protect endpoints from malicious executable files, which are the least sophisticated form. Some of the most advanced and targeted attacks arrive in the form of seemingly harmless data files that are opened by legitimate applications. For example, malicious code can be implanted in a Microsoft Word or PDF document- also known as an exploit. Traps protects endpoints by preventing malware in the form of executables and exploits in the form of data files or network-based attacks. The most advanced threats these days leverage vulnerabilities in software that we use on a regular basis. Once the file is opened, the malicious code takes advantage of a vulnerability in the legitimate application being used to view the file, allowing it to execute code and take full control of the endpoint.
How Exploit Prevention Works
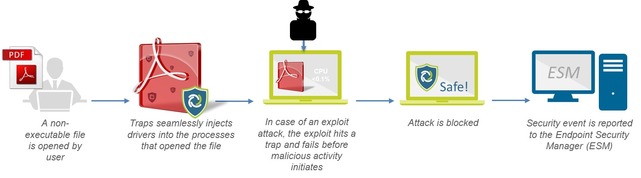
Regardless of the attack or its complexity — in order for the attack to be successful the attacker must execute a series exploit techniques in sequence. Traps employs a series of exploit prevention modules aimed at mitigating and blocking the different exploit techniques available to attackers. Furthermore, each exploit needs to use a series of those techniques in order to be successful. Traps renders these techniques completely ineffective, which means the application is no longer vulnerable. The Traps agent injects itself into each process as it is started. If the process attempts to execute any of the core attack techniques, the exploit attempt will fail because Traps had made the process impervious to those techniques. Traps will immediately block that technique, terminate the process, and notify both the user and the admin that an attack was prevented and report all of the details to the Endpoint Security Manager (ESM).
But unlike other products, Traps is not limited to protecting only those processes or applications. By focusing on the exploit techniques and not the attack itself, Traps can prevent the attack without prior knowledge of the vulnerability, regardless of patches in place, and without signatures or software updates. It’s important to note that Traps isn’t scanning or monitoring for malicious activity, so there’s a massive scalability benefit to this approach as very little CPU and memory are used.
Preventing Malicious Executables
In addition to preventing exploits, Traps employs a multi-layered approach to the prevention of malicious executables by focusing on three key areas to ensure comprehensive protection. When combined, these methods offer unparalleled malware prevention and include:
1. Policy-Based Restrictions: Organisations can easily set up policies restricting specific execution scenarios. For example, you may want to prevent the execution of files from the Outlook tmp directory, or prevent execution of a particular file type directly from a USB drive.
2. Advanced Execution Control: Traps execution control provides granular control of global policies to control child processes, folders, unsigned executables, etc. as well as system hardening capabilities by allowing granular control over which applications or hashes should or should not be allowed to run.
3.WildFire™ Inspection & analysis: Traps queries the WildFire threat cloud with a hash and submits any unknown .exe files to assess their standing within the global threat community.
4. Malware Techniques Mitigation: Traps implements technique based mitigations that prevent attacks by blocking techniques such as thread injection.




